Blogs.

A new paradigm to extinguish cyber risk for good: 24/7 protection connects with cyber insurance
...

Eliminating cyber risk for your clients together
Businesses built on partnership In the relatively short time we’ve been in...
Product Update: Demo Portal
In this blog, we sit down with Anne Postma, our Product Manager, to discuss the...


Product Update: Vulnerability & Threat Hunting
In this blog, we interview Robbin Begeer, Product Manager at Eye Security,...
CrowdStrike Falcon and Microsoft blue screen issue updates
Last updated: July 30th at 00:00 CEST In this blog, we provided real-time...

NIS2 Directive Overview: In-depth look at Articles 21 and 23
While many EU countries are still working out the specifics of implementing the...


NIS2: How the New EU Cyber Law Protects Your Business
Cyber attacks are now big business – but they’re impacting smaller companies....


NIS2 EU: Top 3 Cyber Laws and Their High-Level Definitions
Cybersecurity compliance can seem daunting. With so many new regulations coming...

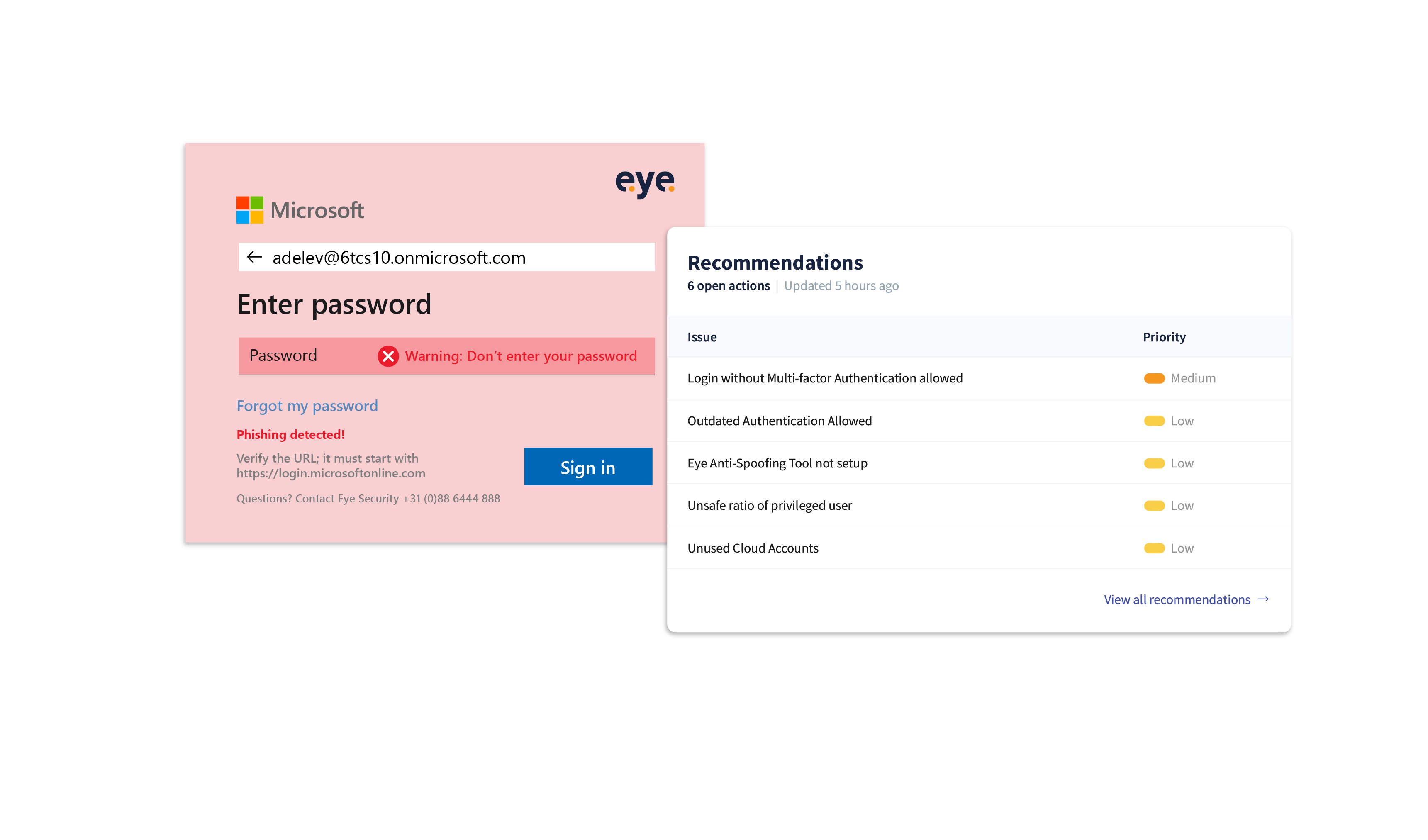
Empowering security: the battle against Login Spoofing
Introduction Battling cyber-crime can sometimes feel like an endless tennis...

A Conti-nuous issue
Introduction In this blog, we shed light on our findings during a forensic...

