Blogs.

How Microsoft might have lured unsuspecting end-users into the hands of criminals
...


Top 5 Cyber Threats Manufacturers Face in 2025
Cyber attacks can be devastating to manufacturers. They disrupt supply chains,...

Manufacturing and Cybersecurity: What Are the Challenges?
Manufacturing companies form the very foundation of the global economy....

A new paradigm to extinguish cyber risk for good: 24/7 protection connects with cyber insurance
...

Eliminating cyber risk for your clients together
Businesses built on partnership In the relatively short time we’ve been in...
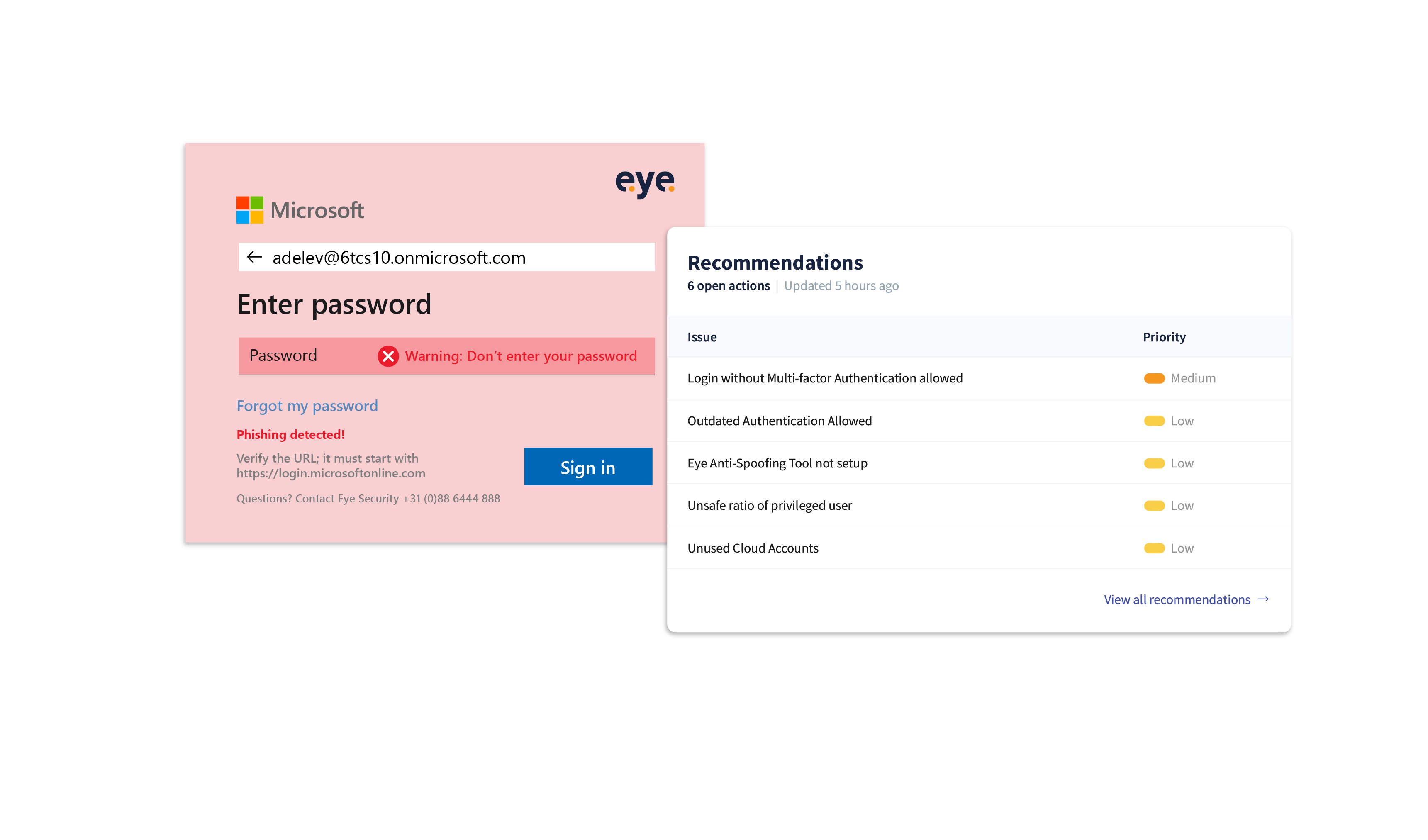
Empowering security: the battle against Login Spoofing
Introduction Battling cyber-crime can sometimes feel like an endless tennis...

A case of ransomware, resolved
...

Logistics cybersecurity in 2024: Hello new growth! Hello new risks...
Sustainability. Growth. Digitalisation. These are the words everyone's using...

Microsoft Teams Phishing: How to Stop The Rising Phishing Threat
Introduction Around mid-September, our Security Operations Centre (SOC)...

The silent crisis: IT burnout due to increased cybercrime
Employee absenteeism is rising among IT managers and employees, as are burnout...

NIS2: how will it be transposed in European countries?
The NIS2 Directive is the latest European cybersecurity regulation, aiming to...
